In this series of blogs we examine all topics under the information security umbrella (including phone fraud). From corporate blunders to rogue state attacks to the occasional celebrity hack, we believe there is something for businesses and individuals to learn from any cyber security event. We also believe that, while experience is the best teacher, it’s even better to let other people make the mistakes for you.
In this series of blogs we examine all topics under the information security umbrella (including phone fraud). From corporate blunders to rogue state attacks to the occasional celebrity hack, we believe there is something for businesses and individuals to learn from any cyber security event. We also believe that, while experience is the best teacher, it’s even better to let other people make the mistakes for you.
We are coming to you with a topic very important to us- telephone fraud. The ranges vary but overall phone fraud is an enormously costly drain on the telecom industry. It totals over $46 billion dollars in 2013 alone. Yes, that’s with a “b.” We care about this topic because the majority of the fraud is committed against small businesses. That is because they lack the resources that larger organizations employ to protect their systems. We’re not okay with criminals attacking our family. We’ve put together some best practices on how to protect ya neck. We do not take too kindly to attacks on our family.
Wait, Crime Isn’t New?
People have been committing phone fraud crimes since phones had access to technology. Originally referred to as Phone Phreaking, the first widespread recognition of this type of offense. They used devices referred to as boxes and differentiated by their method of attack designated by colors. Criminals used everything from Red Boxes that would simulate the sounds of coins entering into early payphones. They did this to register false payments to the more widely known Blue Box. The Blue Box would emit a 2600hz tone to pirate the long-distance capabilities of a targeted telephone number.
Broader Reach, Bigger Problem
Modern telecom evolved from relatively simple beginnings where tonal deceptions could be chaotic for telephone systems. Over time it evolved away from those risks. These vulnerabilities were eventually identified and corrected. The new world of hosted telecom began to open up shortly thereafter. Thus providing new territory for lawlessness to try phone fraud.
This virtual landscape continues to keep a very close watch on its borders. A spike in an industrious criminal organization came with rises in phone technology. Most hosted telecom companies know this and have invested heavily in safeguarding their phone network. This process is costly and requires nuanced, expert knowledge to execute. Where does that leave you? Without a Concierge to guide you through the ins and outs of telephone security, it’s difficult. We’ve put together a few pointers on how to stay safe.
Know Where the Exits Are At All Times
If you can ascertain how and where a thief will try and gain access to your network, you also know where to build your awareness. Here are a few of the most common types of phone fraud on modern telephone systems.
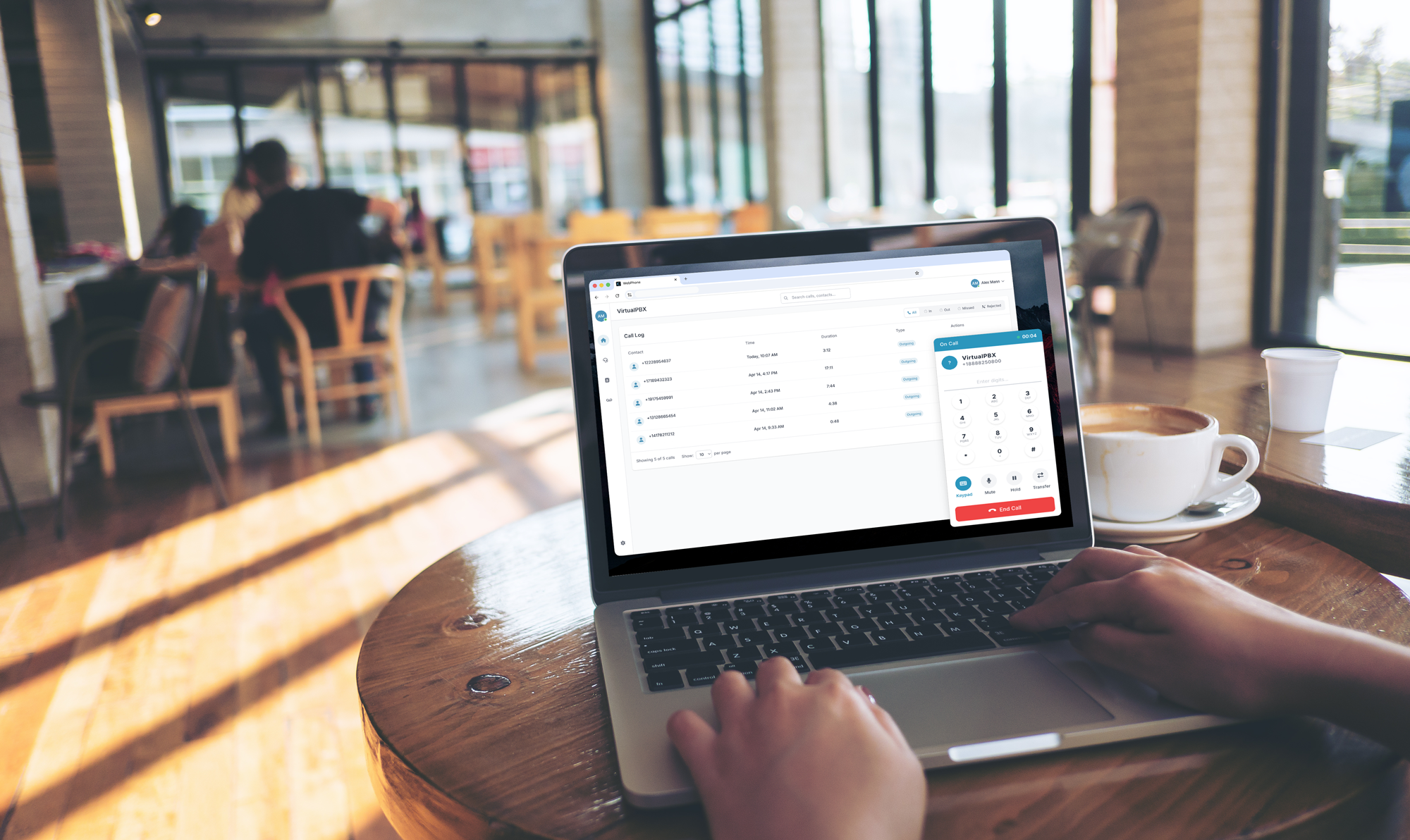
- PBX Registration Exploitations – This is when malicious attempts to register devices are made to your network. If they are successful they can remotely call out from your system racking-up charges.
- Hardware Attacks – VoIP phones actually operate with pared-down versions of many of the desktops and laptops that power businesses. If they are compromised, they can be programmed to route all calls through external, usurious numbers.
- The Long Con – One of the greatest vulnerabilities for thieves is through your own employees. If not properly versed on phone fraud, your team can let slip vital information that can be used against the whole company.
These are the most common ways for VoIP systems to be attacked. While the extent of damage is greater with these powerful networks, the opportunities for graft are abundant, too. With even a little bit of resistance, criminals are likely to give up quickly on phone fraud.
Suit-Up In Armor
Not as dramatic as gearing up for a joust, but hoisting some protection will go a long way in defense of phone fraud. Taking these steps will prove to be a robust beginning layer of any comprehensive data-security plan for your company.
- Monitor device registration frequencies. Even with many mobile devices being used by your team in the field, you should always have a good idea of how many registries you’d have in total. Wild variations or spikes in that number could indicate that an attempt to breach your network has been made.
- Another way to protect devices on your network is to always make sure that they are behind a firewall.
- Update your billing contact information to the appropriate stakeholders. Often times, IT staff will be the initial employees on technical accounts whereas you may want a controller or AP manager to hold access to them after they’re established.
- Update your system preferences to reflect a minimum amount of access. To combat against malicious auto dialers make sure that calls are routed after a period of time from the menu, otherwise they can cycle indefinitely and charge and crowd your network.
- Establish meaningful access restrictions to the administrator level of your phone network by granting admin authority only to the people who actually need it. Also, educate all employees on what their individual access means and the proper protocol for protecting it.
- Make sure to run the latest versions of all the software and firmware your company needs to keep moving. Updates are often ignored when they don’t have noticeable changes. By ignoring updates, you’re potentially missing out on critical patches that can be critical for keeping you protected.
- And finally, the vast majority of hacks begin with poor password strength. Maintaining strong password protection is indispensable.
In Conclusion
We’d love to tell you that your network is always going to be safe from phone fraud, but that’s just not responsible thinking. The best way to make sure that you stay safe in the long run is to do what you can in the short-term whenever you employ a new technology. Whether it’s a VoIP phone at your office or a new computer at your desk, begin that relationship with a healthy, thorough process of security protocol and you’ll find that your need for ongoing protection and damage control will likely be much less than if you hadn’t.
If you need any more specifics about this or another unified communications security topic, our data-security experts are always available to help. If you’ve gotten what you need today, make sure to pay it forward and share this with others who could use it.
Stay safe out there and remember to Protect ya Neck from phone fraud!