 Today’s password misconceptions guest post was written by TechWarn, a digital safety advocate and news site.
Today’s password misconceptions guest post was written by TechWarn, a digital safety advocate and news site.
We use passwords every day. In fact, the average Internet user has 90 online accounts which likely means they’re using nearly a hundred passwords as well. But even though passwords are the main security measure in the digital world, most people know very little about password strength and how to maximize their protection. Even more surprising, a lot of people hold completely false misconceptions about passwords.
Let’s dive in and debunk some of the most common ones.
Misconception 1: Password Protection Is Enough
Passwords might be the most common way to secure your accounts, but they’re by no means foolproof. Password cracking software is widely available on the dark web, allowing even amateur hackers to break through security. No matter your password strength, you can also fall victim to phishing or other social engineering attacks in which hackers trick you to voluntarily reveal your credentials.
Let’s face it: on their own, passwords never offer a sufficient level of protection for your sensitive data.
It’s a good idea to add two-factor authentication for extra protection. Two-factor authentication is a combination of something you know (password) and something you have (ex. your phone). Even if the hacker cracks your password, they will still need the other half of the key to get into your account. Most of the time, this should be sufficient to keep them away.
Note that not all two-factor authentication methods are equally secure. There is a consensus among cybersecurity experts that SMS messages are the weakest second authentication step. Through social engineering, the attacker can redirect the victim’s texts to his own SIM card and intercept the messages. That’s why the recommended method is either using an authenticator app on your phone (ex. Google Authenticator) or a physical security key.
Misconception 2: Passwords Should Be Memorable
At face value, this password misconception makes perfect sense. You’re not supposed to write passwords down so, of course, they must be memorable enough to simply remember them. Right?
Not quite. No matter how memorable your passwords are, it’s still not possible to remember dozens of them (as I mentioned before, you likely have around 90 accounts to secure).
The best way to handle your passwords is to get a password manager. A password manager is a program that securely stores all your login credentials and other sensitive information. It’s also an incredibly handy tool for teams as you can organize your passwords and give other team members access.
If you have a password manager, there’s no need to remember any passwords except your master key to access the manager. That password should definitely be memorable, but none of the others need to be.
Misconception 3: Passwords Can’t Contain Dictionary Words
There’s an ongoing debate among cybersecurity experts about this one. Some claim that passwords consisting of a random string of letters, digits, and characters have the highest password strength. Others argue that a cluster of dictionary words, such as “correcthorsebatterystaple” can be just as strong while being a lot easier to remember.
So which one is it?
Let’s conduct an experiment. Using a password security tool, I checked a four-word passphrase “raviolijakartacrabhamlet” against a random 20-character password generated by my password manager “0zut07IcAT8D65n28Ys4”. The result for the former was 7 quadrillion years, while the latter would take 558 quadrillion years to crack. When I shortened my random password to 15 characters, however, the time to crack it decreased to 609 million years.
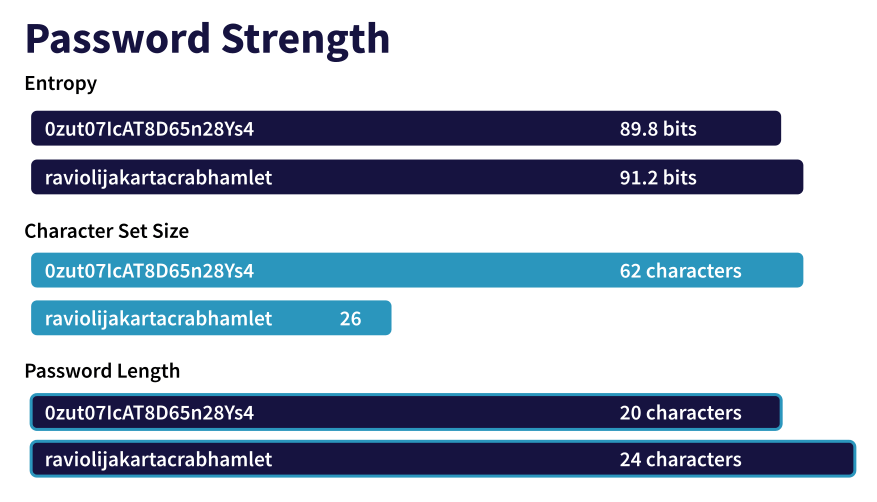
This discrepancy depends on the entropy (or complexity) of the password, which includes length and character sets as factors. If you’re willing to work with extremely long, 20-character passwords then, indeed, those are more secure than passphrases. The shorter ones, however, seem to lose when compared to random word clusters.
In the grand scheme of things, it doesn’t matter too much anyway because we’re talking millions of years to crack the password. It’s worth pointing out, though, that as the technology develops, the time to crack complex passwords will decrease. What might take millions of years today, might take just weeks in a few years and maybe mere seconds a decade from now.
Misconception 4: Some Characters Are Disallowed
Passwords can, in fact, include any characters. Emojis can also be part of your password and the password manager company Myki has even released an emoji-only password generator.
However, some people learned the hard way why emojis in passwords are not a good idea when they tried logging in with a keyboard that doesn’t support emojis. With little evidence as to whether emoji passwords are more secure or easier to remember, it’s probably better to steer away from them for now.
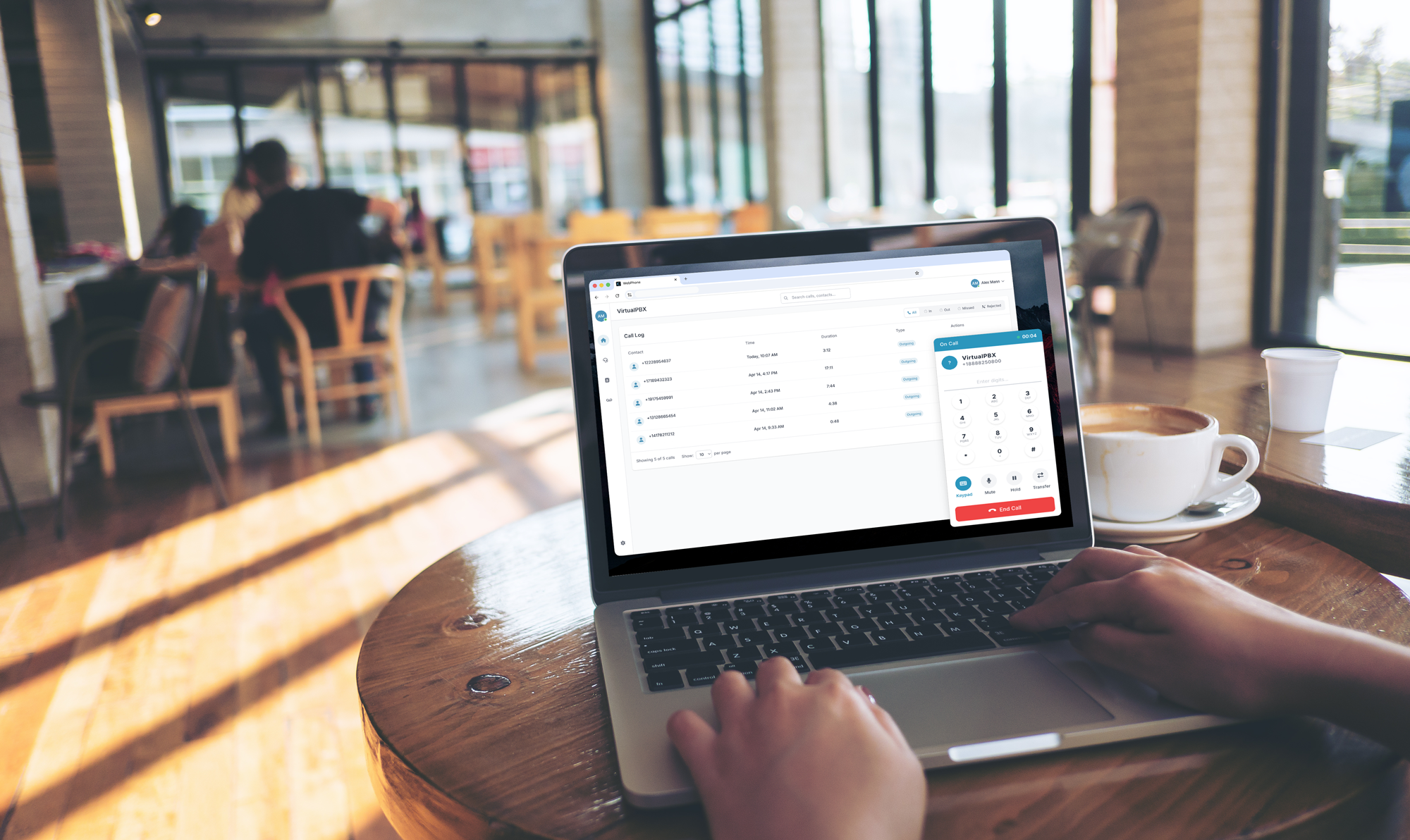
Your VirtualPBX Account
VirtualPBX emphasizes data security in all aspects of its phone system. Its users play a strong role in the security of their own accounts, so it’s suggested that strong passwords be used for all admins and users on its phone plans. For assistance with creating new passwords or to inquire about account security, reach out in a live chat.