
The Essential Guide to Call Center Agent Duties: Mastering Customer Service Excellence
Explore the Essential Call Center Agent Tasks of Answering Calls, Mastering Product Knowledge, Multitasking, Time-Management, and More In


Explore the Essential Call Center Agent Tasks of Answering Calls, Mastering Product Knowledge, Multitasking, Time-Management, and More In

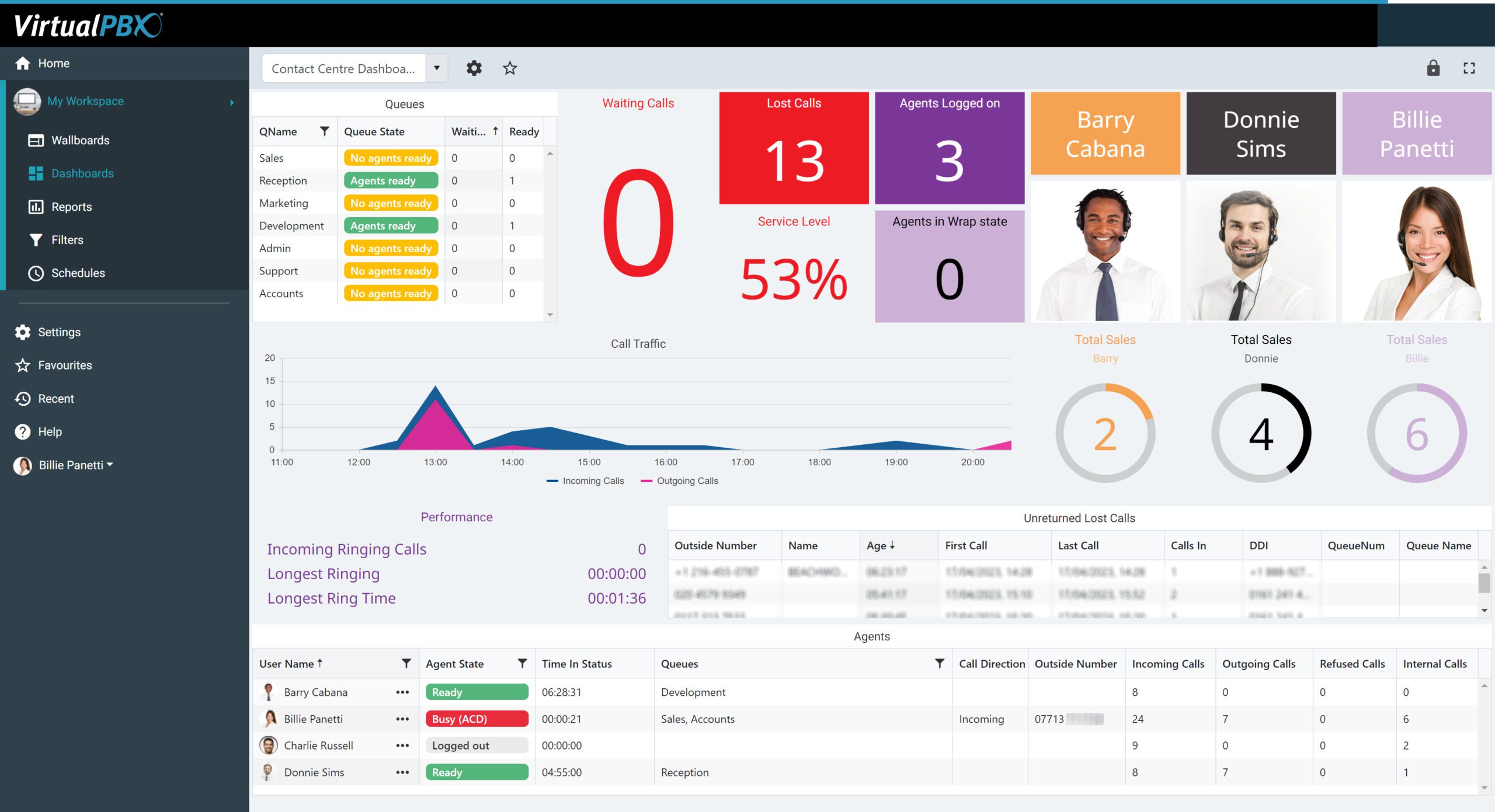
Deliver The Industries Best Customer Service With Seamless Integration And Reports VirtualPBX Contact Center is thrilled to introduce

Last week we announced the newest product to our lineup The VirtualPBX Contact Center. But what is a
In today’s lightning-fast business ecosystem, where time is the ultimate currency, delivering exceptional customer service isn’t just a

Ensuring safety in public spaces is paramount. One of the cornerstones of public safety is the presence of

When the tax season rolls around, businesses are faced with the crucial task of meeting their tax filing
In the era of rapidly advancing communication technologies, it’s crucial to understand the foundations upon which our modern

We are thrilled to announce that VirtualPBX has been honored with the prestigious 2024 Product of the Year

In the ever-evolving landscape of telecommunications, businesses must stay vigilant to adapt to regulatory shifts that can impact
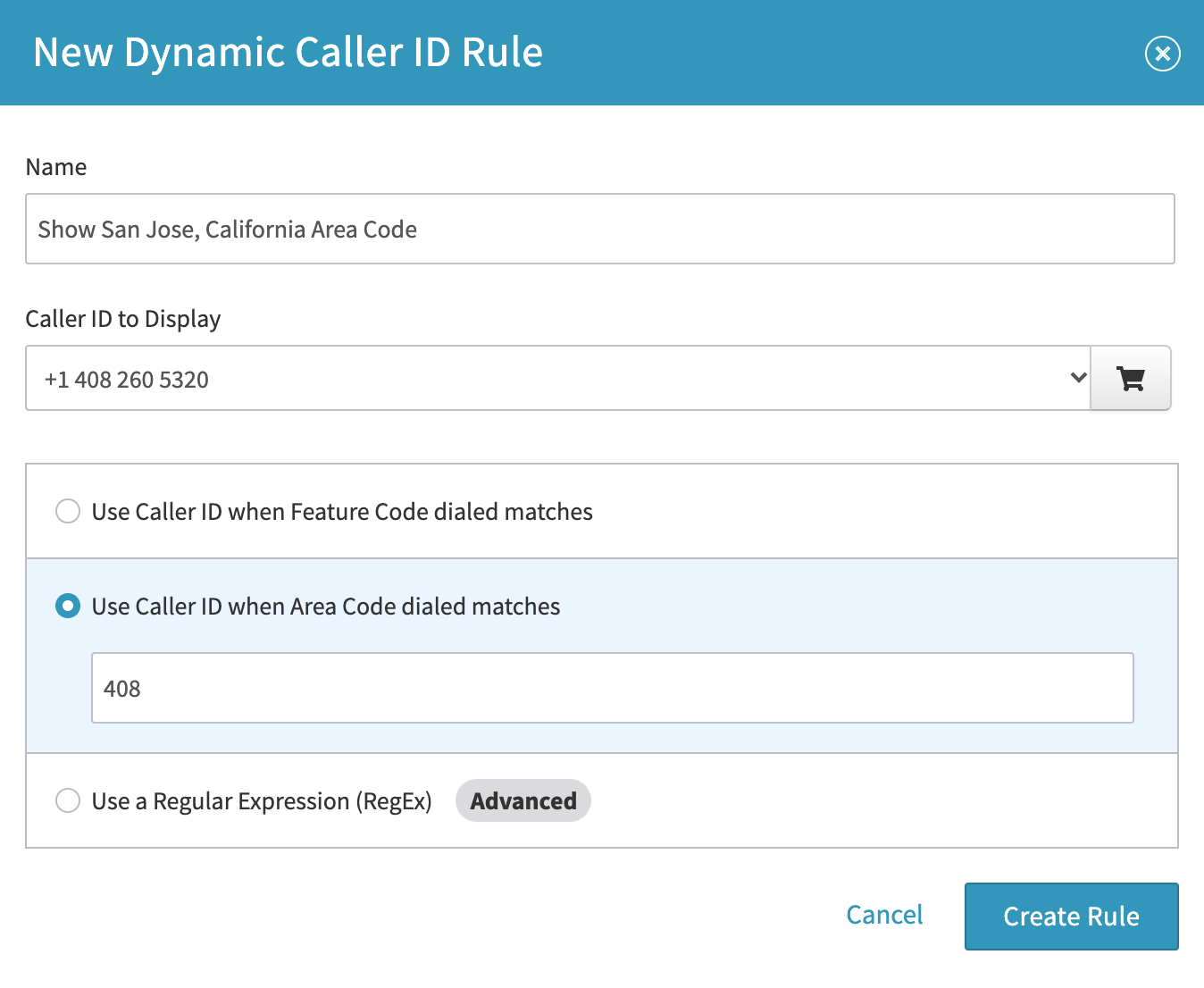
In the business world, every interaction counts. Whether you’re reaching out to potential clients, following up with leads,

In the fast-paced and ever-evolving landscape of modern business, effective communication stands as an indispensable cornerstone. Whether you’re

In the rapidly advancing era of high-speed internet, fiber optics, and cutting-edge telecommunications technologies, it’s easy to overlook

1998-2024. VirtualPBX.com, Inc. All rights reserved. VirtualPBX, TrueACD, and ProSIP are ® trademarks of VirtualPBX.com, Inc.