What is PSTN & how does it work
In the era of rapidly advancing communication technologies, it’s crucial to understand the foundations upon which our modern

In the era of rapidly advancing communication technologies, it’s crucial to understand the foundations upon which our modern

In the ever-evolving landscape of business, knowledge is power. Every entrepreneur, whether seasoned or aspiring, understands the importance
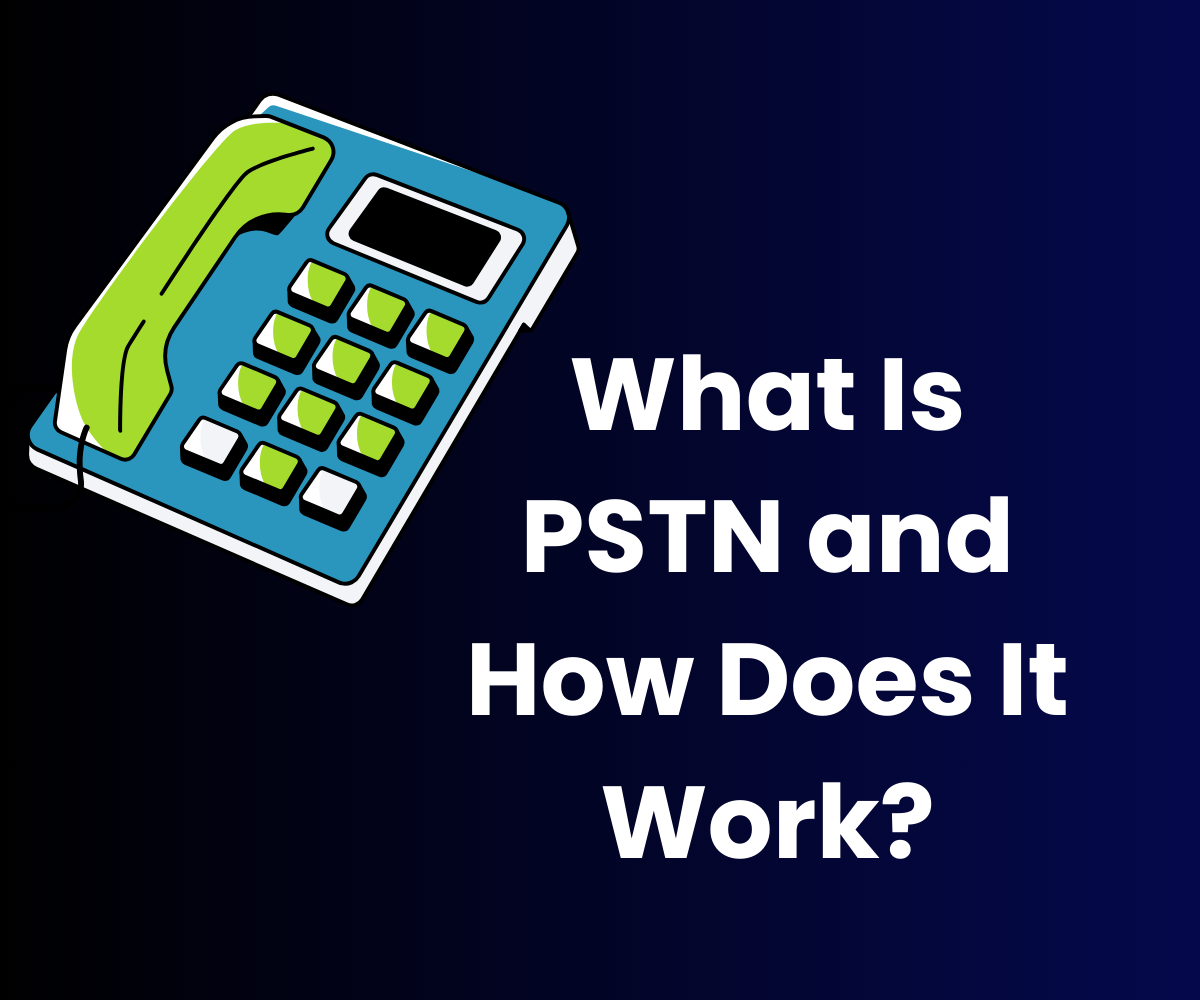
Effective call center management is paramount to ensure customer satisfaction and operational efficiency. Fortunately, advancements in technology have

In today’s digital age, businesses are more reliant than ever on technology to streamline operations and communicate with
The All-New Strategy Hub for VirtualPBX Customers If you’ve landed on our blog, you’re probably already aware that

Voice over Internet Protocol (VoIP) has revolutionized communication, enabling voice calls over the internet and reshaping connectivity. As

As the summer season approaches, businesses are actively seeking ways to reduce operating costs while maintaining efficient communication
T-Mobile home internet users have faced frustrating limitations when it comes to utilizing VoIP services. T-Mobile restricts VoIP
VirtualPBX is committed to delivering the latest and most innovative technologies, including AI for business, to ensure that

As of October 1st, 2022, The Centers for Medicare & Medicaid Services (CMS) is requiring that all calls

Unplanned emergencies due to inclement weather and other situations can happen anytime. Unfortunately, most businesses don’t think about

For many professionals and larger businesses, fielding over 20 business calls in a day is an easy task.

1998-2024. VirtualPBX.com, Inc. All rights reserved. VirtualPBX, TrueACD, and ProSIP are ® trademarks of VirtualPBX.com, Inc.